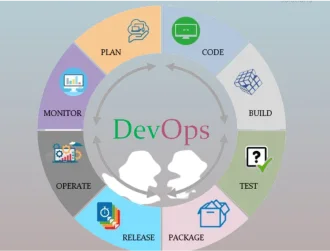
01Securely scale and accelerate DevOps process.
After getting a lot of benefits, organizations seek to expand the adoption of DevOps in their operation. However, the processes and tools that work for small-scale operations usually fall short when organizations try to scale their DevOps operations. Today’s development and operations teams need to automate things and deliver fast. The DevOps team should not waste time due to the manual, slow processes. They need to move fast, but security teams struggle to keep up with them. Implementing DevOps at scale requires the right processes, structure, tools, and security measures.
Where scaling and speed become important factors, the security activities in DevOps processes are overlooked or deprioritized. However, security should be an integral part of the entire DevOps process, from the beginning to the end. Organizations can opt for DevOps consulting services or hire DevOps consultants for secure scaling and acceleration of their DevOps processes. In this article, we will outline the five key steps to scale and accelerate DevOps processes securely and efficiently.

Let’s get started.
02 Central management of end-to-end DevOps processes.
An end-to-end primary DevOps platform must include management of container images, binaries, security and compliance, CI/CD pipelines, and software distribution to the last-mile deployments across runtime environments. Many CI/CD tools allow you to manage automation processes and help you avoid configuration drift. It’s important to have a DevOps platform allowing the central artifact management using a single solution. It speeds up software delivery, optimizes code quality, governance and security, and lets you scale and accelerate efficiently.
03Version control.
It’s a practice to manage code in versions, track change history and revisions to review the code easily, and then recover. Version control is implemented via version control systems, such as Git, enabling developers to collaborate in authoring code. The system provides a clear vision to code changes happening in the same file and handle conflicts. The use of version control is a basic DevOps practice building the foundation for automated deployments. However, adopting version control puts pressure on the DevOps teams to maintain system scalability and security. There is a need to implement robust security measures.
04Security with built-in DevSecOps and ‘Shift left’ technique.
Organizations should incorporate compliance and security measures across the entire software development lifecycle (from development to deployment and production). Leveraging services from third-party vendors come with a lot of security risks, such as security misconfigurations and vulnerabilities, license compliance issues, and other governance risks. There is a need to patch these vulnerabilities more often and try to stay ahead of criminals. For this, companies have to implement security and compliance, perform deep and recursive scanning that should be continuous and automated. Moreover, implement a shift-left approach to identify and patch vulnerabilities. The sooner they detect the vulnerabilities, the easier it is to fix them.
Read about Challenges in DEVOPS Implementation
05 Pipelines-as-code.
The ability to implement pipelines-as-code enhances the developers’ productivity and helps to scale DevOps processes. Store the pipeline definitions in the source control, making them shareable, usable, version-able, and auditable. It eliminates redundant work and enables standardized and vetted automation processes across the organization. It increases speed and productivity via sharing of automation building blocks, such as processes, resources, security tests, policies, configurations, and more. Moreover, it improves security, governance, and quality by standardizing on hardened, approved processes across the organization.
06Continuous monitoring.
It’s a practice that helps to ensure the security of scaled DevOps. Continuous monitoring is considered a threat intelligence method that automates the monitoring of vulnerabilities and controls to support organizational risks management decisions. Good continuous security monitoring can provide visibility on all assets across the organization, such as cloud storage, mobile applications, web applications, IoT and connected devices, public code repositories, and email servers.

Also Read
Case Study to Step by Step process to building an Automated CI-CD Pipeline in IOS Application Deployment with DEVOPS Operations.
Final words
DevOps teams are responsible for selecting the right tools and delivery infrastructure to provide DevOps-as-a-service for internal teams with standardized processes, shared tools, and consistent governance. With scale and growth in DevOps processes, many organizations think that it’s difficult to implement security measures. In this article, we have discussed a few best practices to securely scale and accelerate DevOps processes.